
Need a way to prevent VPNs from running on your network? We get why. On a home network, you can use it as a way to ensure that parental controls are enforced. In a workplace or educational environment such as school or university, the situation is similar. It’s a great way to make sure students or employees stay focused. Additionally, preventing the use of a VPN allows has security benefits. You can force users to stick to the rules that forbid certain access, especially to websites, app stores, or video streaming services. Simultaneously, you can prevent the installation of third-party VPN apps. With some of the benefits mentioned, let’s get into how to block a VPN.
Clarification. We’ll be using an ASUS Wireless router firmware for demonstration. If you are using Netgear, TP-Link, Linksys, D-Link, or any other manufacturer, the names of options should be almost identical. You can always check the official website or look through router settings on your own.
Why are VPNs blocked?
While VPNs are legal in some places and not so much in others, we have seen a trend where more and more websites and organizations have started to actively block VPNs, irrespective of their legality. Thus, we have explored the various reasons behind such blocking and listed them in the following section.
Legal issues
First up is the self-evidentiary legal trouble. If the country or the government has declared VPNs to be illegal, then it is up to the ISP in the region to enforce the rule. Thus, they employ VPN blocking. Websites and other internet services within these regions also have to take measures to stop VPN access.
Government Censorship
Then there is always censorship. Even without outright banning some content, governments do censor the internet as they see fit. However, a VPN is capable of bypassing these blocks. Thus, they ban VPNs themselves to stay ahead.
Workplace restrictions
Workplaces, schools, and other similar organizations use firewalls on their networks to prevent unauthorized internet use. They do not want the employees or students to be wasteful and spend their time surfing irrelevant websites. And since a VPN can easily bypass network restrictions, they often use VPN blocking.
Copyright and Licensing issues
And finally, we have copyright and licensing problems. A content creator, be it an individual or a corporation, has digital ownership of its content. Hence, they can choose to restrict a region from accessing their product. It is done through licensing to generate more profits. But a VPN can bypass geo-blocks. Hence, these corporations invest in technology that can block VPNs.
Methods to Block a VPN
1. Block the website URL or keyword
This method won’t block a VPN from working. On the other hand, it will prevent network users from downloading a VPN app or visiting websites required for setting up a remote VPN server. Keep in mind, this won’t work on websites that use an HTTPS protocol, or utilize HTTP compression due to encryption. Here’s how to forbid access to an URL or keyword on an ASUS router:
- Open your default browser.
- Enter 192.168.1.1 or http://192.168.1.1 (default ASUS IP router IP address) in the address bar and press Enter.
If that doesn’t work, the easiest way is to enter http://router.asus.com for routers or http://repeater.asus.com for ASUS range extenders. - Enter your administrator username and password. It is admin/admin by default.
- After you log in, click on Firewall under Advanced Settings in the menu on the left on the left.
- Go to the URL Filter tab.
- Scroll down and enter a website in the URL Filter List column. For example, www.vpnsitename.com
- Click on the + icon in the Add/Delete column.
- Click on the circle in front of Enabled under Enable URL Filter.
Can I block keywords?
Certainly. Blocking keywords is done from the Keyword Filter tab next to it. You can add keywords such as “VPN”, “proxy”, “unblock” “streaming” etc.
2. Block an IP address
Using a hostname won’t work with websites utilizing an HTTPS protocol, which is a rapidly growing number. Luckily, all websites have an IP address that is translated into the hostname by a DNS server. Once again, this won’t prevent users with a VPN or proxy from circumventing restrictions but prevents them from obtaining VPN applications or VPN server settings.
Finding a website IP address
There are ways to do this on Windows, macOS, and Linux that utilize Command Prompt or Terminal. This is faster and easier since your browser is already open. Do this to lookup an IP address of a website:
- Visit a page such as Site24x7’s Find IP Address.
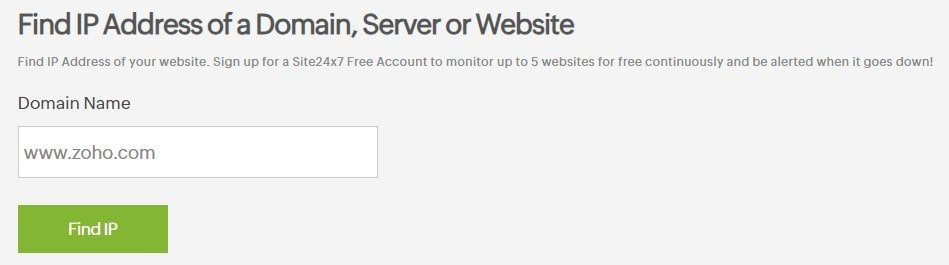
- Enter a domain name and click on Find IP.
- Copy the IP address, for example, 15.15.15.15, and proceed to the next steps.
How to block an IP address
If you closed the tab, log back on the router settings page. Then, follow these steps to forbid an IP address on the router’s network:
- Click on LAN under Advanced Settings.
- Go to the Route tab.
- Select Yes under Enable static routes.
- Under Network/Host IP, paste the IP you found above.
- As Netmask, enter 255.255.255.255.
- For Gateway, use your router’s IP, e.g. 192.168.1.1 by default.
- As Metric, enter 2.
- For Interface, select LAN.
- Click on the + under Add / Delete, then click on Apply.
- Repeat this step for as many IP addresses as needed.
- Optional. Open Terminal on Mac or Command Prompt on Windows. Enter ping + IP address above, e.g. ping 15.15.15.15, and press Enter. If you get “Timed Out” or “Destination Host Unreachable” it was successful.
3. Use NAT Passthrough to block a VPN
This is an easy way to forbid VPN access by preventing the VPN connection to pass through the router and connect to the Internet. It will prevent NAT (Network Address Translation) from modifying the information in the IP header. With that said, here’s how to disable NAT Passthrough on an ASUS router:
- Access your router configuration home page.
- Under Advanced Settings on the left side, click on WAN.
- Switch over to the NAT Passthrough tab at the far right.
- You need to change settings for PPTP Passthrough, L2TP Passthrough, and IPSec Passthrough.
- Click on the down arrow next to Enable, and change it to Disable.
- Click on the Apply button at the bottom.
- Tip. If other protocols appear after a firmware upgrade (IKEv2 or SSTP, for example), you should come back and repeat these steps for them.
What to do if network users still use VPNs
This is common. As we mentioned, not all security protocols are supported or added in firmware. Additionally, VPN providers are slowly implementing proprietary protocols, such as ExpressVPN’s Lightway, NordVPN’s NordLynx, or HotspotShield’s Catapult Hydra. ASUS and other router manufacturers are highly unlikely to add them. For both of these reasons, we decided to showcase the method below.
4. Forbid certain ports from passing through the router to block a VPN
First, we’ll show you where to find ports, then how to utilize what you learned. Let’s jump right in.
How can I find a list of ports VPNs use?
You’ll have to do a little research. Start with the commonly used security protocols such as IKEv2, SSTP, OpenVPN, or L2TP. Do you know the VPN provider used by people you want to block it for? Check their official website for ports they utilize. To help you, we made a quick ports list, sorted by security protocols, under method 5 in our “how to hide a VPN” guide. Never block ports 443 (SSL/HTTPS) and 80 (websites), since they will prevent connection to a large part of the Internet, VPN or not.
Blocking ports tied to VPN inside the router settings
Once again, open your router configuration page and log in. Now, here’s how to block certain ports via ASUS router:
- Go to Firewall under Advanced Settings in the left-hand side menu.
- Go to the Network Services Filter tab.
- Click on the empty circle in front of Yes under Enable Network Services Filter.
- Under Filter table type, select White List or Black List. Here’s how it works:
- White List. During the scheduled time and days of the week, users can ONLY use specified Network Services e.g. ports, in this case.
- Black List. During the days and time specified, users cannot use specified Network Services (ports).
- Explanation. We’ll use Black List for demonstration since it’s far less restrictive. In a strict work environment, you might find it easier to add a White List, then only enable ports 80 and 443, as well as 25, 465, and 587, which are required for e-mailing.
- Under Well-Known Applications, change User-Defined to WWW.
- Make sure all days of the week are checked under Date to Enable LAN to WAN Filter. Uncheck some if you want to enable VPNs on, for example, weekends.
- Change Time of Day to Enable LAN to WAN Filter if you want to use VPNs outside of work hours, for example. We’ll leave it as 00:00-23:59.
- Leave Filtered ICMP packet types empty.
- Now, move over to the table, and follow these steps:
- Leave Source IP empty, it will be auto-filled if it isn’t already.
- Under Port Range, enter a port. We’ll enter 1723, for PPTP.
- Under Destination IP, enter your router’s IP address. We’ll enter 192.168.1.1
- Under Port Range, we’ll enter 1723 again. You can also enter two ports like this: 1723,1725. It will block both ports and all the ports in between.
- As Protocol, select TCP or TCP ALL.
- Click on the + icon in the Add / Delete column.
- Click on the Apply button.
- Tip. If the VPN uses the same port on both TCP and UDP protocol, you have to repeat steps 1 through 4, then choose UDP under Protocol in a new table row.
- Repeat this for as many ports as needed. On our router, the maximum is 32 entries, which is plenty.
